Category: User Privacy
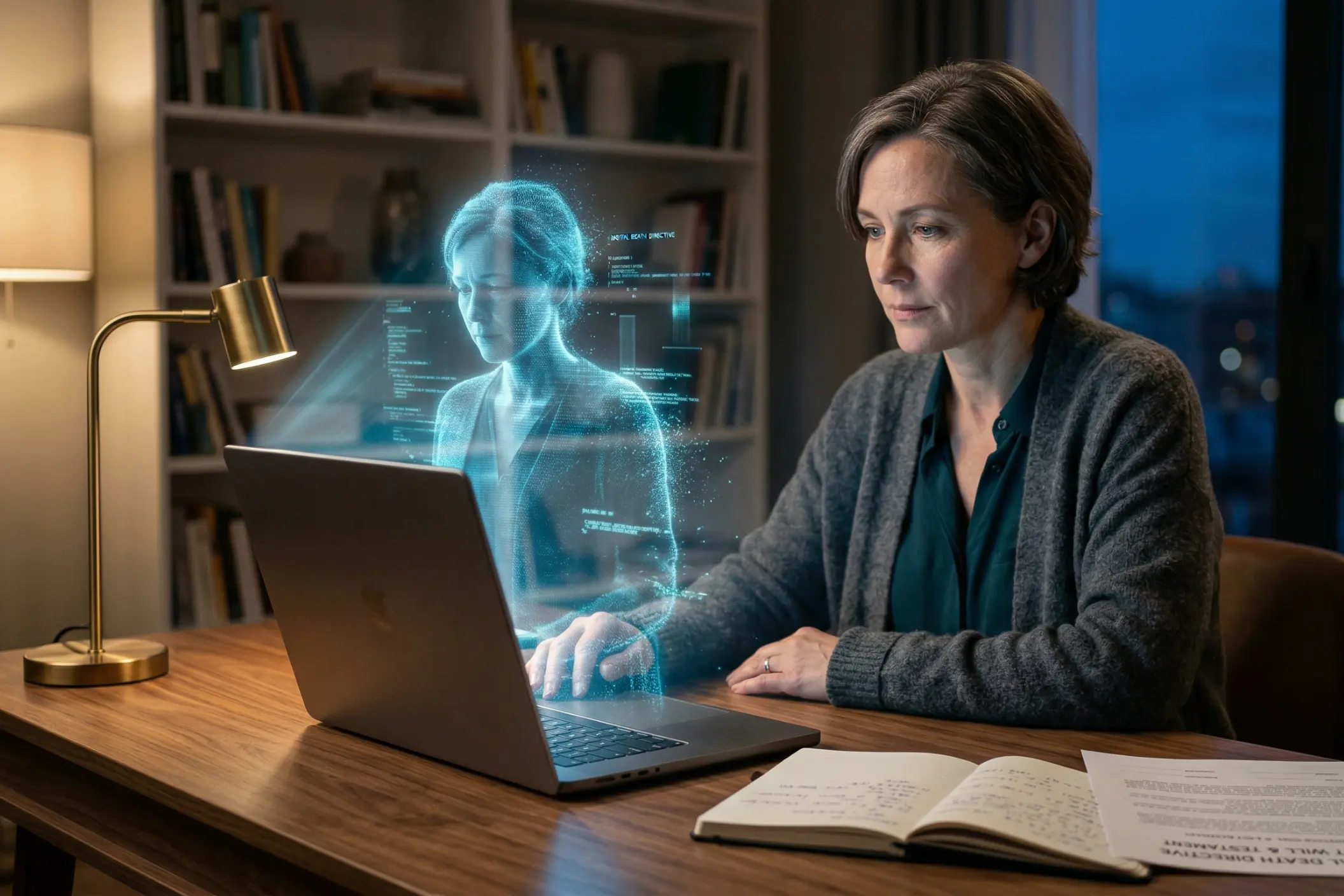
Digital Death Directives: How to Stop Posthumous AI Doppelgangers
March 25, 2026
The afterlife has officially relocated. It now lives on servers.
What used to be a purely spiritual concept has collided head-on with artificial intelligence, spawning a frankly bizarre, multi-billion-dollar market dubbed “grief tech.” This booming sector takes cutting-edge generative algorithms and uses them to resurrect the dead digitally speaking. Software can now map the exact voice, facial tics, and conversational habits of someone who recently passed away. The result is a highly interactive, slightly unsettling avatar that texts, speaks, and reacts from beyond the grave.
Sure, this technology brings a strange sort of solace to some grieving families. But it also rips open a massive ethical and legal black hole. As the software gets cheaper and sharper, building a posthumous “digital doppelgänger” is no longer just a weird plotline from a late-night sci-fi show. It is happening right now. That harsh reality explains exactly why modern estate planners are aggressively pushing a vital new tool for everyone’s administrative toolkit: the Digital Death Directive.
The Rise of “Grief Tech” and the AI Afterlife
Families used to rely on dusty photo albums, fading polaroids, or old voicemails saved on a carrier network just to remember a loved one. Generative AI completely shattered that old dynamic. Mourning is rapidly shifting from remembering someone quietly to actively chatting with their digital ghost.
Startups and massive tech conglomerates alike are clawing for a piece of an estimated $126 billion death tech industry. And the mechanics are shocking in their simplicity. Users just dump audio files, old text threads, angry emails, and vacation pictures into a proprietary model. Almost instantly, the machine spits out a convincing voice clone or a deepfake video. These so-called “deadbots” actually study a person’s specific sense of humor. They learn their slang. Surviving relatives can literally text a synthetic version of the person they buried last week and get back an eerily accurate response.

Developers keep filing patents for wild new integrations, too. Some experimental designs even let algorithms hijack a deceased user’s social media feeds, posting memories and commenting on photos exactly like the living person used to do. It is a stunning technological leap. It is also an absolute minefield.
The Ethical Minefield of the Digital Doppelgänger
Just because a developer can code a digital soul does not mean anyone actually should.
Getting a morning voice note from an AI replica of a late spouse might offer a temporary emotional crutch for people struggling through raw grief. Yet, psychologists are increasingly sounding the alarm. Leaning too heavily on a machine often short-circuits the natural human mourning process. It traps vulnerable people in a loop, fostering an unhealthy dependency on a bot that feels absolutely nothing.
Then, you hit the legal nightmare. The laws surrounding digital resurrection are practically nonexistent. A handful of states have passed post-mortem privacy laws, but those generally just protect famous celebrities from unauthorized commercial deepfakes in movie trailers. For everyday citizens? There are virtually no rules. Nothing stops a distant cousin, a rogue app developer, or a scam artist from scraping a dead person’s public online life to build a clone.
Imagine the potential fallout. A grieving widow opens her smartphone to a synthetic voice message from her late husband, cooked up by well-meaning friends who accidentally caused severe emotional trauma instead of providing comfort. Worse still, cybercriminals clone a voice using public TikTok videos to bypass biometric banking security and drain dormant checking accounts. Without explicit, legally binding instructions left behind, families walk into this digital chaos completely blind.
Enter the “Digital Death Directive”
Standard estate planning relies heavily on a Last Will and Testament to hand out tangible objects houses, cars, vintage watches, and cash. But traditional wills completely ignore the massive, sprawling digital footprints people drag behind them today. That is exactly where the Digital Death Directive takes over.
Think of it as a highly specialized addendum to a will, or a standalone legal document, that dictates precisely how a digital legacy gets handled when the heartbeat finally stops. Above all else, it plants a firm legal flag regarding consent. It specifically outlines the total refusal or permission for posthumous AI recreation. Drawing clear boundaries protects the deceased’s identity while sparing exhausted heirs from making impossible, agonizing choices during a funeral.

Key Elements of a Comprehensive Digital Death Directive
To make sure a tech company or a family member actually follows these digital wishes, the document needs a few non-negotiable pieces built directly into its framework:
1. Explicit Consent or Refusal for AI Recreation
The single most critical clause today tackles artificial intelligence head-on. The paperwork must clearly state if personal data can be used to train voice clones or video avatars. If the answer is yes, the document must specifically name who gets to pull the trigger and what exact software platforms they are legally allowed to touch. If the answer is no, the language must slam the door completely shut, forbidding anyone from twisting the person’s likeness into a chatbot.
2. The Appointment of a Digital Executor
Physical wealth needs a standard executor. Digital estates require a Digital Executor. This specific person gets the legal green light to act as a digital bouncer. They manage, download, or completely nuke digital assets, acting as the ultimate enforcer for the directive’s rules.
3. Data Destruction vs. Data Archiving
Everyone hoards weird digital baggage. Unflattering search histories, awkward direct messages, hidden photo vaults, and rough drafts of emails. The directive tells the Digital Executor exactly what to save for the grandkids and what to permanently burn. Many people strongly prefer a total post-mortem data wipe to keep their secrets safely hidden.
4. Social Media Memorialization Protocols
Social profiles essentially serve as modern-day gravestones. The directive must decide if accounts on platforms like Facebook, Instagram, or LinkedIn should vanish completely into the ether or shift into locked, official “Memorialized” modes where nobody can log in and post new content.
5. Access to the “Seed Phrase” and Financial Tech
For anyone holding cryptocurrency, NFTs, or decentralized assets, standard banking rules simply do not apply. Sliding a death certificate across a desk to a bank teller will not unlock a Bitcoin wallet. The directive has to map out exactly how to find hardware wallets and private keys. Without those exact seed phrases, the funds disappear into the blockchain forever, totally unrecoverable.
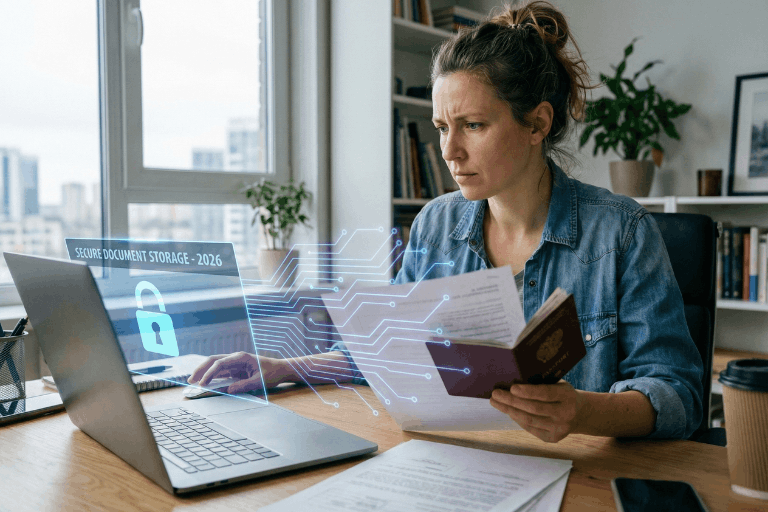
The Importance of Secure Storage
Writing the document is really only half the battle. Storing it poorly makes the entire effort totally worthless.
Decades ago, families stuffed important papers into bank safe deposit boxes or heavy, fireproof home safes. But the digital age moves way too fast for physical brass locks. A bank vault is totally useless on a Sunday night during a sudden medical crisis in a different time zone. Furthermore, static paper documents cannot keep up with the endless password updates and new account creations that define modern internet usage.
Proper estate planning demands modern storage solutions. Critical documents belong in an encrypted, independent cloud environment. That setup guarantees the Digital Executor and trusted partners can grab the directive the exact second they need it, no matter where they happen to be standing.
Taking Control of the Digital Hereafter
The line separating life, death, and data gets blurrier every single day. As tech companies relentlessly push the envelope of what is scientifically possible, protecting a posthumous identity falls entirely on the individual. A Digital Death Directive is no longer a quirky, niche tool for tech nerds. It is a fundamental necessity for anyone with a Wi-Fi connection.
By locking down these difficult decisions today, individuals guarantee that a digital doppelgänger will never hijack their life’s true legacy. Taking action now allows the real memory to finally rest in peace.
Take the Next Step to Uncomplicate Life: Ensure loved ones never have to guess or fight about a digital legacy. Take 10 minutes today to draft a Digital Death Directive and upload it securely to the InsureYouKnow.org Electronic Safe Deposit Box, where it remains encrypted, protected, and instantly accessible to trusted partners when they need it most.
2026 Student Loan Defaults: Secure Your Financial Records
March 6, 2026
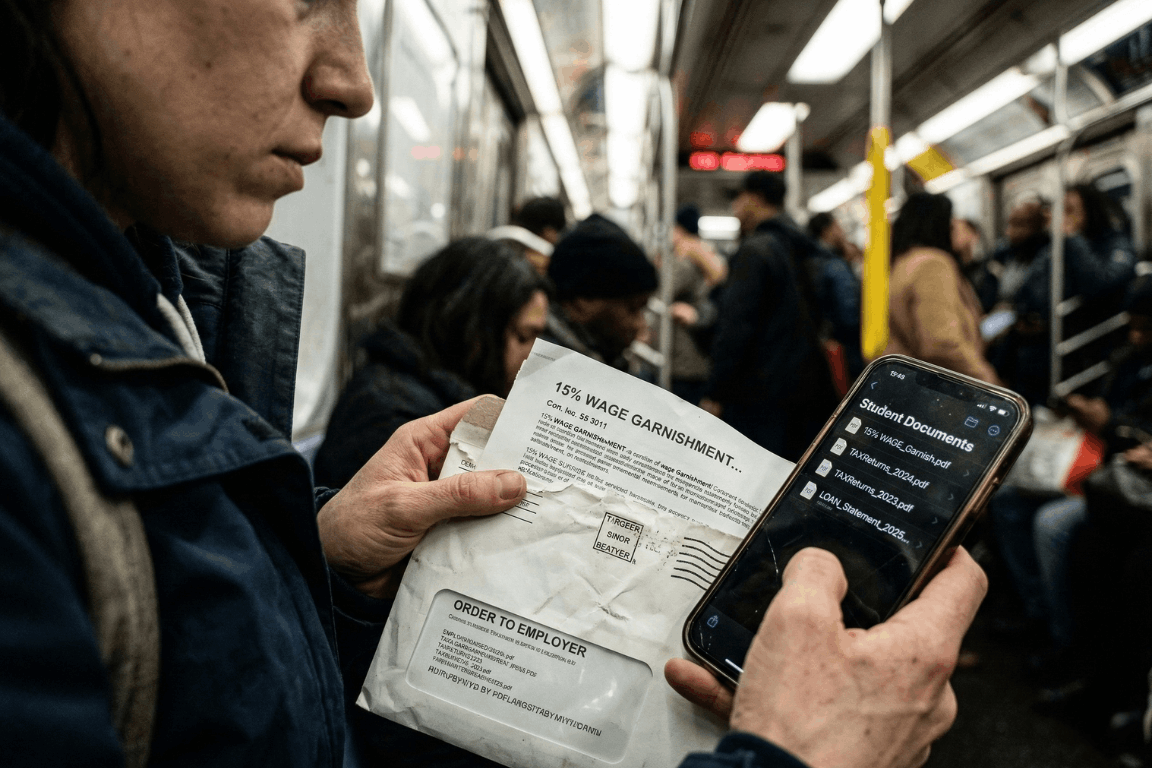
A massive financial wall hit millions of Americans earlier this year. Pandemic payment pauses are officially ancient history. The temporary relief programs dried up entirely. After months of messy court battles regarding income-driven repayment plans, the federal government decided to bring back its heaviest collection tools. Starting in early 2026, the U.S. Department of Education began sending administrative wage garnishment letters to defaulted borrowers. The numbers from major credit bureaus, like Experian, look pretty grim. The entire country is watching a massive wave of loan delinquencies happen in real time. People are suddenly staring down severe financial penalties. Getting through this economic squeeze requires a lot more than just reading news updates. It demands immediate, highly organized access to specific financial paperwork.
The 2026 Student Loan Landscape: A Shocking New Data Trend
So, who is actually defaulting right now? Historically, student loan defaults mostly hammered sub-prime borrowers. That whole narrative flipped completely upside down in 2026. Recent reports from credit bureaus reveal something entirely unexpected. Nearly a quarter of newly defaulted borrowers belong in the “prime” credit tier or even higher. These are the exact demographics the financial industry usually views as incredibly stable.
With over 5 million borrowers currently sitting in default status, and millions more falling behind every month, the economic pain is obvious. Borrowers are stuck navigating a bizarre maze of constantly changing payment plans. Making things worse, millions of accounts got bounced around between different private servicing companies over the last two years. Monthly payments got lost in the mail. Crucial paperwork simply vanished. Hold times to speak with basic customer service stretched into hours. Once a federal student loan reaches 270 days past due, it hits official default status. At that specific moment, the government gets to use an administrative superpower that regular credit card companies cannot even touch. They can literally take wages without ever stepping foot inside a courtroom.
Understanding Administrative Wage Garnishment: The 15% Reality
The fallout from a federal default happens fast. Through a process called Administrative Wage Garnishment (AWG), the Department of Education can legally force an employer to pull up to 15% of a borrower’s disposable pay. Disposable pay simply means the cash remaining after legally required deductions, like federal and state taxes, come out of the check.
Federal law does leave a very small safety net in place. Borrowers get to keep a weekly take-home amount equal to at least 30 times the federal minimum wage. But for anyone living from one paycheck to the next, suddenly losing 15% of their income is pure disaster. It usually means missing the rent, skipping the grocery store, or defaulting on other credit cards. Before the garnishment actually kicks in, the government must send a 30-day advance written warning. That specific 30-day window is basically everything. It acts as the only real timeframe a borrower gets to object or set up a different payment plan before their paycheck actually shrinks.
How to Stop Garnishment: The Heavy Burden of Proof
Borrowers holding a garnishment notice still carry some legal rights. During those 30 days, individuals can officially demand a hearing to stop the withholding order. They might attempt to prove extreme financial hardship. Or, they could try applying for federal loan rehabilitation. Rehabilitation usually involves agreeing to make nine on-time payments over a 10-month window to get the loan back on track.
Another route involves submitting a formal financial hardship appeal. Winning this appeal means legally proving that a 15% pay cut makes buying basic survival items impossible. The government looks at documented living expenses and compares them against very strict IRS Allowable Living Expense guidelines. If a family spends more on food or housing than the IRS thinks is necessary for that specific family size, the extra amount gets totally ignored. Proving hardship is notoriously difficult. Using these rights is never a walk in the park. It requires gathering highly specific legal and financial records immediately. In these types of administrative hearings, the burden of proof lands squarely on the borrower.
The Critical Role of Organized Financial Documents
Sloppy paperwork turns a bad money situation into an absolute nightmare. When the garnishment letter shows up, the clock ticks fast. Spending hours digging through cluttered email inboxes for old messages from loan servicers wastes valuable time. Tearing up the living room looking for utility bills to prove basic living expenses just fuels the anxiety. If a borrower fails to hand over the correct evidence within 30 days, their employer receives the order. The garnishment starts.
This explains exactly why relying on a secure, independent electronic safe deposit box changes the playing field. Keeping a dedicated digital vault for vital life information ensures nobody gets blindsided by aggressive debt collectors. Storing all important financial, legal, and contractual documents in one simple location gives borrowers a huge advantage. They can instantly grab the exact proof they need to protect their paychecks and negotiate with default resolution teams.
Essential Documents to Secure in a Digital Vault
To build a strong defense against a default warning, individuals should make sure the following documents are digitized, safely uploaded, and ready for action:
- Original Loan Agreements and Master Promissory Notes: Finding original contracts immediately helps verify the true debt amount. It also spots accounting errors and confirms which company actually owns the loan today.
- Complete Tax Returns: Proving financial hardship or enrolling in an income-driven repayment plan means submitting paperwork. The Department of Education demands recent federal and state tax returns before they even start talking.
- Official Pay Stubs: Current pay stubs are absolutely required to figure out actual disposable income. They also help verify that any proposed wage garnishment does not illegally drop below the minimum wage protection limit.
- Household Expense Records: Tracking basic living costs is a strict requirement for hardship appeals. Think about rent agreements, mortgage papers, utility bills, health insurance premiums, and pharmacy receipts. These papers help prove that living expenses are reasonable and fit within tight IRS standards.
- Correspondence with Loan Servicers: A strong paper trail of older payments, approved forbearances, and emails with the loan servicers can literally save the day. This proof is extremely important if someone needs to show a loan was wrongfully thrown into default in the first place.
The Absolute Security of Zero-Knowledge Storage
Privacy is absolutely non-negotiable when dealing with highly sensitive financial details. Relying on physical metal filing cabinets leaves people wide open to lost papers, house fires, or basic theft. Depending on regular, unencrypted email folders or a messy computer desktop basically hands sensitive financial data directly to hackers. Cybercriminals routinely target email servers specifically to find W-2 forms and tax returns. Once they grab those files, identity theft is pretty much guaranteed.
Using a specialized platform built with heavy-duty cloud encryption makes sure financial data stays completely private. The absolute best platforms run on Amazon cloud encryption mixed with a “zero-knowledge” setup. In a zero-knowledge system, only the actual account owner knows the password. The site administrators never get to see it. That means absolutely nobody else can ever gain access, view the files, or mine the stored documents to sell the data.
Strategic Document Sharing with Trusted Partners
Fixing a defaulted student loan is almost never a solo job. Borrowers usually need to bring in certified financial planners, tax accountants, or specialized student loan lawyers to help decode the messy federal rules.
Advanced secure portals allow individuals to selectively share specific document folders with these exact trusted partners. Sending unencrypted PDFs of tax returns and pay stubs back and forth through regular email is a massive cybersecurity hazard. Instead, account holders can simply give a legal advisor temporary, secure access to the required files right inside the encrypted vault. This targeted sharing feature speeds up the whole default resolution process, keeps communication secure, and leaves the rest of the vault totally locked down. Setting up automatic monthly reminders inside the portal also helps users routinely update their financial snapshots, keeping their defense strategy completely fresh.
Facing economic uncertainty requires a solid game plan. The return of federal student loan wage garnishments in 2026 creates a massive hurdle. Credit bureau data clearly shows that financial distress is hitting borrowers across every single demographic right now. Surviving this wave of defaults demands aggressive, proactive money management and flawless record-keeping. Centralizing vital financial documents into a secure, encrypted digital safe deposit box lets individuals tackle economic chaos with total confidence. Being prepared is simply the ultimate defense. It ensures that when critical financial information is needed the most, it stays protected, perfectly private, and instantly ready to use.
Passkeys vs. Passwords: Why It’s Time to Switch Now
February 26, 2026

We all do it. Every morning. You grab your coffee, sit down, and try to log into your bank. Or maybe your insurance portal. You type in a password. Maybe it’s a strong one. Maybe it’s… well, let’s be real. It’s probably the same one you use for Netflix. But here is the hard truth: relying on a secret code just doesn’t cut it anymore. Not when your entire financial life is sitting behind it. Fast forward to 2026, and there is finally a better option that people are actually using: the passkey.
If you are the one stuck managing the heavy stuff for your family – wills, health records, the “in case of emergency” file – knowing the difference between a passkey and a password isn’t just tech trivia. It is a survival skill. It’s about keeping the wolves at the door away from the things that actually matter.
This guide breaks down exactly what passkeys are, how they smash the old-school password system, and why making the switch is probably the smartest move you can make right now.
What Is a Password – And Why Is It No Longer Enough?
Think about it. A password is just a string of letters you made up. It’s a secret handshake between you and a computer. And for a long time? That was fine.
But here is the snag: humans are involved. And humans? We are messy. The stats are pretty rough – something like 70% of hacks start because of a weak or stolen login. We reuse passwords because we’re lazy. We pick easy ones because we’re forgetful. Or we get tricked by a fake email and hand them over on a silver platter.
Common password headaches include:
- Brute-force attacks: Hackers have computers that can guess billions of passwords a second. If yours is simple, it’s gone before you can blink.
- The Dark Web: If one random site you use gets breached, your password ends up for sale. Suddenly, the bad guys have the keys to your whole life.
- Phishing: It is terrifyingly easy to get fooled by a fake email or website that looks real. You type it in, and poof – they have it.
- Fatigue: You have dozens of accounts. Remembering unique codes for all of them? Impossible. So we reuse them. And that is dangerous.
- SMS flaws: Even those text message codes aren’t bulletproof. Hackers can swap SIM cards and steal those codes right out of the air.
There is a saying in the security world that haunts me: Hackers don’t break in – they log in. If they have your password, they are you.
What Is a Passkey – And How Does It Work?
Passkeys are a total rewrite of the rules. Forget typing. A passkey uses public-key cryptography. Imagine a digital key that is split in two. One half sits on the website. The other half stays locked inside your phone or laptop.
When you want to log in, your phone and the website have a quick, silent chat. You prove it’s you by just unlocking your screen – Face ID, fingerprint, whatever. You don’t type a single letter. Nothing gets sent over the internet for a hacker to steal.
Think of it like a puzzle. The website has a piece. Your phone has a piece. They only fit together when you – the real you – are holding the device.
Key facts about passkeys:
- They run on the FIDO2 standard. Basically, the big tech companies all agreed on a better way to do things.
- Everyone is jumping on board: Google, Apple, Amazon, Chase Bank. They all support it.
- Millions of people are already using them without even realizing it.
- You can’t phish them. You can’t guess them.
- If you have a smartphone from the last few years, you are already ready to go.
Passkeys vs. Passwords: A Side-by-Side Comparison
Why is everyone making such a big deal about this? You have to look at the differences side-by-side to really get it.
1. Security
- Passwords: Weak. They can be stolen, guessed, or fished out of you with a fake email.
- Passkeys: Rock solid. The private key never leaves your phone. Even if a hacker breaks into the bank’s server, they can’t steal your key because it isn’t there.
2. Ease of Use
- Passwords: A pain. You forget them. You reset them. You type them wrong.
- Passkeys: Easy. You look at your phone, or touch the sensor. Done. It works 98% of the time and it’s way faster.
3. Phishing Resistance
- Passwords: Terrible. If a fake site looks real, you’ll probably type your password in.
- Passkeys: Perfect. A passkey is tied to the real website. If you land on a fake site, your phone knows. It simply won’t let you log in.
4. Device Dependency and Flexibility
- Passwords: You can use them anywhere, but that’s also why they are risky.
- Passkeys: They live on your device. But don’t worry – Apple and Google sync them to the cloud. So your passkeys are on your phone, your tablet, and your laptop automatically.
5. Risk in a Data Breach
- Passwords: If a company gets hacked, your password is leaked.
- Passkeys: If a company gets hacked, the hackers get… nothing useful. They just get a public key that can’t unlock anything without your phone.
Why This Matters for Protecting Vital Life Records
We usually don’t think about this stuff until it’s too late. You get hacked, or a family member passes away and nobody can get into their accounts. That is a nightmare scenario.
The accounts that hold your life’s work – insurance, savings, wills – need better protection than “123456.” If these get breached, it’s not just annoying. It’s identity theft. It’s losing money.
The banks know this. That’s why Chase and Wells Fargo are pushing passkeys. They want you safe.
If you are using a digital vault to keep your family’s info organized, turning on passkeys is the single best thing you can do today.
How to Set Up a Passkey (It Is Simpler Than It Sounds)
You don’t need to be a tech wizard. It takes two minutes.
Step 1: Go to your account settings (Google, Amazon, whatever).
Step 2: Look for “Passkeys” or “Security.”
Step 3: Click “Create Passkey.” Your phone will ask for your face or fingerprint. Do it.
Step 4: You’re done. Next time, just click “Use Passkey.”
Step 5: If you want to be extra safe, use a password manager like 1Password to keep them all organized.
Expert Tip: Start with the big ones. Email. Bank. Insurance. Get those locked down first.
Should Passwords Be Abandoned Entirely?
Not yet. We’re in a transition phase. Lots of old websites still need passwords. So here is the game plan:
- Switch to passkeys for anything important.
- Use a password manager to generate crazy long passwords for the junk sites that don’t support passkeys yet.
- Stop using SMS codes if you can help it. Use an app instead.
- Get a hardware key (like a YubiKey) if you are really paranoid about your email security.
- Check back often. More sites are adding this every month.
Microsoft went passkey-first last year and it’s been huge. By the end of 2026, typing passwords will feel like using a flip phone.
What Happens If a Device Is Lost?
Everyone asks this. “If I lose my phone, am I locked out forever?”
No. You’re fine.
- Cloud Sync: If you use an iPhone, your keys are in iCloud. Get a new phone, sign in, and they are back. Same for Android.
- Backup: You can still use other ways to get into your account if you absolutely have to.
- Thieves can’t use them: Even if someone steals your phone, they don’t have your face or fingerprint. They can’t use your passkeys.
Passkeys and the Future of Secure Document Storage
For families storing wills and financial docs online, security is everything. A digital vault is pointless if the key is under the mat.
Passkeys fix the human error part. You can’t accidentally give away your passkey. It solves the biggest problem in security: us.
Experts at Gartner and big tech firms are calling this the biggest shift in security in decades. The password era is ending. Finally.
Key Takeaways
- Passwords are weak. They are too easy to steal or guess.
- Passkeys are strong. They use heavy-duty encryption and your own biometrics.
- It’s happening now. Major banks and tech giants are already using them.
- Mix it up. Use passkeys where you can, strong passwords where you must.
- Don’t worry about lost phones. Cloud sync has your back.
- Protect your legacy. If you store vital records, this is a must-have upgrade.
Conclusion: The Lock Is Getting an Upgrade
Switching to passkeys isn’t just about cool new tech. It’s about peace of mind. Passwords put all the pressure on you to be perfect. Passkeys let your device handle the security so you don’t have to.
If you are serious about keeping your family’s future safe, stop waiting. Passkeys are here. They work. And they are way better than what you’re using now.
The best time to switch was yesterday. The second best time is today.
Protect What Matters Most
InsureYouKnow.org provides a secure, encrypted electronic safe deposit box for life’s most important information – insurance policies, financial records, healthcare documents, and more. Storing vital records in one organized, protected location means families are never left searching when they need information most. Start protecting what matters today at InsureYouKnow.org.
AI and Data Privacy in 2026: Securing Vital Information
February 19, 2026
Forget the old sci-fi movies. Today, artificial intelligence practically runs the show. It handles everything from spotting diseases to balancing checkbooks. Every major industry uses these tools to save time and cut corners. But there is a massive catch. This entire system runs on one specific fuel. That fuel is personal information.
Understanding how these powerful computer networks handle private details matters more today than ever before. The tech moves incredibly fast. The ways companies grab and store digital footprints change right along with it.
The AI Data Appetite: How Information is Used
Machine learning models are hungry. These systems require an unbelievable amount of raw material to actually function. Sometimes, a program chews through billions of data points just to learn a single, simple pattern. A fast screen swipe, a late-night online purchase, or a routine doctor’s chart update, they all leave a permanent mark.
Code then sifts through this massive pile of details to customize what people see online. Sure, that makes picking a streaming movie or getting a quick cash loan way easier. But it comes at a cost. Big corporations constantly harvest and tag private details. These software tools connect the dots between things that seem totally unrelated. Next thing you know, a retailer is predicting what a customer will buy next Tuesday, or even guessing their secret health conditions.
Emerging Privacy Risks in the AI Era
This massive leap in technology brings a totally new set of privacy headaches. People have to deal with these threats every single day.
- Sophisticated Cyber Threats: Hackers rarely waste time guessing passwords anymore. Why bother? They use generative code to craft perfect phishing emails and hyper-realistic deepfakes instead. These modern scams blow right past old-school security filters. Because of this, bank records and identities sit directly in the firing line.
- The Rise of “Agentic” AI and Shadow Apps: Smart software agents operate on their own now. They move files and make choices at crazy speeds. When employees or everyday folks rely on unregulated “shadow” tech tools, highly sensitive documents often bleed right into public training models. The worst part? Nobody usually notices until the damage is fully done.
- Algorithmic Bias and Automated Decisions: As computers take over boring office work, invisible biases easily sneak into the mix. A broken piece of code might quietly trash a mortgage application or throw away a great resume. It bases the choice on a hidden profile. The person gets a rejection letter, usually with absolutely zero explanation.
The 2026 Regulatory Landscape
Lawmakers worldwide are finally pushing back hard. This year marks a massive turning point for digital rules and corporate behavior.
Huge rulebooks like the European Union’s AI Act are fully active right now. They slap heavy limits on dangerous technology. Meanwhile, dozens of US states rolled out tough privacy laws that demand total honesty from tech companies. Businesses face strict legal orders to tell the public whenever a machine makes a major choice about a human life. Consumers actually hold real power again. They can demand a look at their files, force fixes, or completely scrub their names from corporate servers.
AI as a Digital Defender
Strangely enough, the exact same tech causing these nightmares also acts as the ultimate shield. Artificial intelligence is completely rewriting the cybersecurity rulebook.
Modern data defense relies heavily on smart threat detection. Clever networks watch internet traffic around the clock. They spot weird behavior and shut down hacks long before human security guards even finish their morning coffee. It also drives better ways to hide identities. Companies can track big shopping trends without ever seeing a specific name or street address.
Strategies for Protecting Vital Information
With the internet getting messier by the minute, folks need solid plans to lock down their critical records. Tossing important papers into a messy email folder or a dusty metal filing cabinet is just asking for trouble. Those old methods simply cannot survive modern cyber attacks. They also fail completely during sudden physical emergencies.
Switching to secure, encrypted digital storage offers a much stronger defense. Platforms offering independent, password-protected electronic safe deposit boxes keep life insurance policies, legal contracts, and medical histories totally out of reach from snooping data scrapers. Putting this vital information inside a heavily locked cloud vault guarantees families can grab exactly what they need during a crisis. At the exact same time, the data stays totally hidden from digital thieves.
The Future of Digital Privacy
The collision between smart machines and data privacy stands as the defining tech battle of 2026. The everyday perks are super obvious. But the background risks demand real attention. Staying updated on legal rights gives regular people a fighting chance. Plus, leaning on heavily encrypted storage for major documents lets individuals walk through this new era safely. Taking a few smart steps right now protects immediate privacy while securing a solid, long-term digital legacy.
Public WiFi vs. Your Data: Why You Need a Secure Vault
January 28, 2026

The Open Window
A traveler sits at a crowded airport gate. The flight is delayed. Boredom sets in. The phone comes out, and there it is: “Free Airport WiFi.”
Click. Connected.
It feels like a small victory. A chance to check a bank balance, pay a credit card bill, or look up a policy number.
But that click? It is the digital equivalent of leaving a house key under the doormat and hoping no one looks.
In 2026, we treat our phones like fortresses. We lock them with faces and fingerprints. Yet, the moment we connect to an open network, we lower the drawbridge. We invite the world in. And the world is watching.
The Invisible Eavesdropper
Here is the ugly truth about public internet: it is loud.
When data leaves a phone on a secure home network, it whispers. On public WiFi, it screams.
The danger isn’t usually some master criminal in a hoodie. It is often just software. Simple, cheap scripts running on a laptop three seats away. These programs are like digital vacuums. They suck up everything floating through the air.
- The Man-in-the-Middle: A hacker cuts in line. The user sends a password to the bank. The hacker catches it, copies it, and then passes it to the bank. The login works. The user has no idea they just handed over their keys.
- The Fake Twin: You see a network called “Coffee_Shop_Free.” It looks real. It isn’t. A scammer set it up five minutes ago. Connect to it, and the device effectively belongs to them until you disconnect.
The “Inbox” Mistake
Fear makes people do silly things. When travelers get nervous about logging in, they turn to an old, bad habit: The Email Search.
“I won’t log in,” they think. “I’ll just find that PDF I emailed myself.”
This is a disaster.
An email inbox is not a safe. It is a glass box. Email accounts are the most hacked targets on the planet. If a thief gets into an email account, they don’t just read letters. They find the tax returns from 2024. They find the scan of the child’s birth certificate. They find the list of “backup codes.”
Using an inbox to store life’s vital documents is like hiding jewelry in a clear plastic bag. It doesn’t work.
The Real Fix: A Digital Vault
So, what is the answer? Carry a filing cabinet? Never go online?
No. The answer is a Secure Digital Vault.
This is where platforms like InsureYouKnow.org step in. They aren’t storage bins. They are armored trucks.
1. It Shreds the Data A real vault uses encryption that mimics the banking world, like Amazon Cloud security. If a hacker snatches a file from the air, they don’t get a readable document. They get noise. A jumbled mess of code that means nothing. The thief gets the envelope, but they can never read the letter.
2. Nobody Knows the Code Privacy matters. The best systems run on “zero-knowledge” rules. That means the company holding the data doesn’t have the password. Even if they wanted to look, they couldn’t. The user holds the only key.
3. Get In, Get Out With a vault, the data lives in the cloud, not on the device. A user can log in on a hotel computer, check a passport number, and vanish. No files left in the “Downloads” folder. No trail for the next guest to find.
Peace of Mind
Security usually feels like a headache. Extra steps. More passwords.
But actually? It is freedom.
It is the ability to lose a wallet in Paris and not fall apart. Why? Because the backup copies of every card and ID are sitting behind an iron door in the cloud. Accessible. Safe. Ready.
Public WiFi is fine for reading gossip columns or checking the weather. But for the heavy stuff like the money, the legacy, and the identity, stay off the open road. Put the valuables in a vault. Lock it up. Then go enjoy the coffee.
Swedish Death Cleaning for Your Digital Life: A Simple Guide
January 15, 2026

The mess you can’t see
There is a Swedish concept that has been making the rounds lately called döstädning. In English, it translates to “Swedish Death Cleaning.” It sounds a bit dark on the surface. Maybe even depressing. But the idea is actually pretty practical: you clear out your physical belongings, the dusty boxes, the clothes that don’t fit, the broken furniture, so your family isn’t stuck dealing with a mountain of junk when you are gone.
But here is the thing about modern life in 2026: the biggest mess isn’t in the garage. It’s floating in the cloud.
People are walking around right now with thousands of blurry photos, email accounts from ten years ago, and passwords that exist only in their heads. It is a silent chaotic mess. And if something happens, that digital chaos becomes a massive headache for the people left behind. Applying a little döstädning to the online world isn’t just about being tidy. It is about saving loved ones from a nightmare.
First, stop the bleeding
Before trying to organize the important stuff, the useless noise has to go.
Think about the average inbox. It is usually stuffed with newsletters that haven’t been opened since 2019 and receipts for things long thrown away. The first step of the clean-up is arguably the best part: hitting unsubscribe. If a subscription hasn’t provided value in the last six months, cut it loose.
Then look at the bank statement. How many streaming services or random apps are charging five dollars a month for nothing? Canceling those doesn’t just save cash today; it stops a confusing financial web from forming later. It is less for the family to untangle.
And then, the photos. Digital hoarding feels safe because it doesn’t take up room in the house. But leaving someone 50,000 screenshots to sort through is rough. Deleting the junk helps the real memories stand out.
The problem with passwords
Imagine cleaning up a whole house, locking the front door, and then throwing the key into a river. That is basically what happens when a digital life is organized but locked down.
In the past, important documents lived in a filing cabinet. A physical key could be found. Today? The “key” is a complex password or a face scan. If nobody else has those credentials, the assets inside, bank accounts, sentimental emails, crypto wallets, might as well not exist. They are locked in a digital vault with no door.
Scribbling passwords on a sticky note is risky. But keeping them entirely memorized is worse.
A smarter way to store it
Once the trash is deleted, what is left? The vital stuff. The deeds, the insurance policies, the wills, the vet records for the dog. These are the papers families panic over during an emergency.
Leaving these files scattered across three different cloud drives and a laptop desktop is a recipe for disaster. The strategy has to shift from “saving” to “managing.”
This is why platforms like InsureYouKnow.org are picking up steam. They aren’t just storage drives. They are digital safety deposit boxes. It gives people a single, encrypted place to put the things that actually matter. And unlike a regular hard drive, it bridges the gap. It keeps the data safe from hackers but ensures a trusted person can actually get to it when they need to.
It answers the question “Where is the policy?” before anyone even has to ask.
A lighter load
Calling it “Death Cleaning” makes it sound heavy. But honestly? It feels more like life cleaning.
There is a real sense of relief that comes from knowing the digital house is in order. No more background stress about lost files or forgotten logins. Just the calm knowledge that if life throws a curveball, the family won’t be stuck fighting with customer support to get into an account. They will have everything they need, right there, ready to go.
5 Scams Targeting Seniors in 2026 (And How to Lock Down Your Data)
January 1, 2026
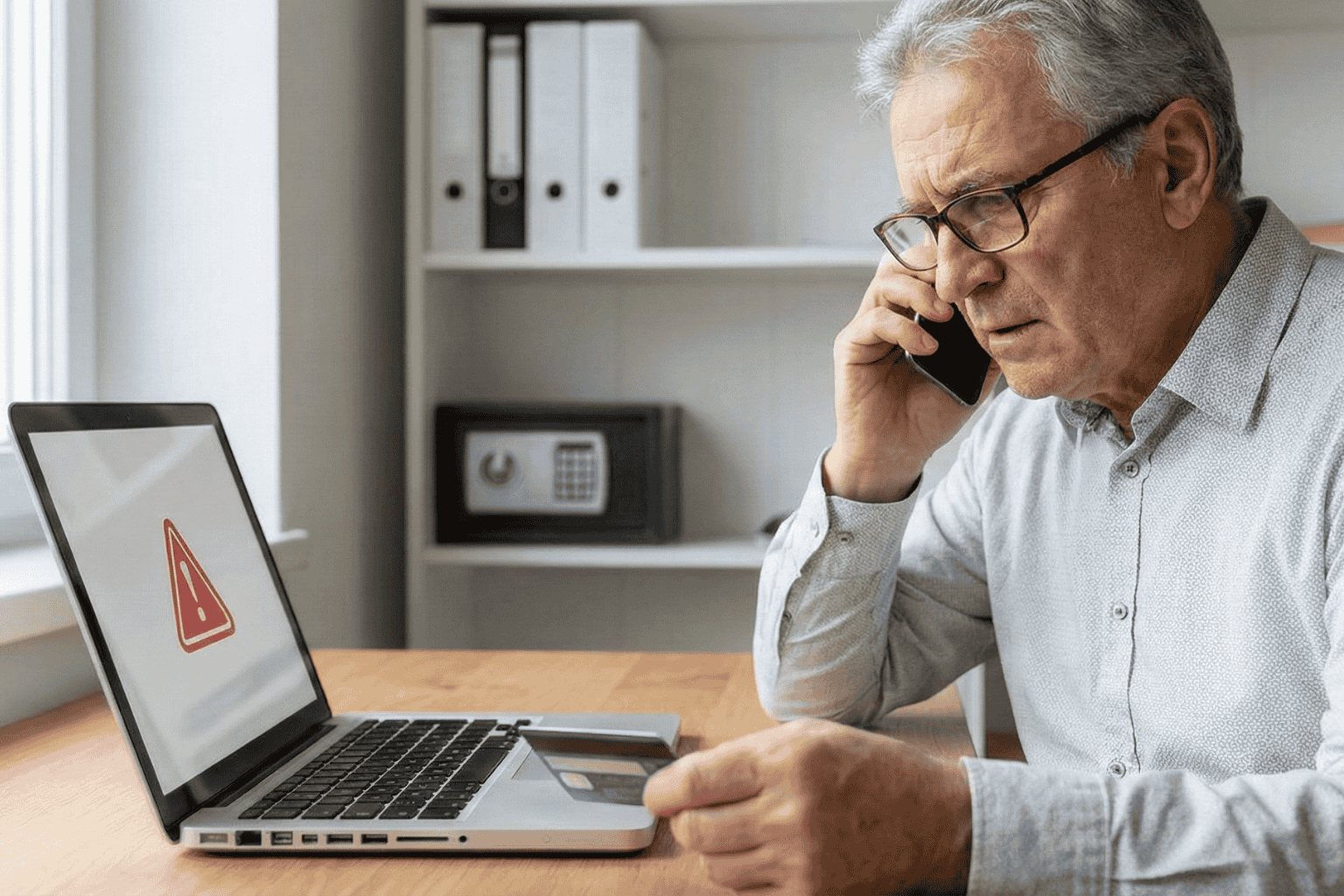
Can you believe it is 2026? We have apps for everything and phones that are smarter than the computers we grew up with. But there is a flip side. All this tech has handed crooks a brand new playbook. And let’s be honest, they love targeting seniors.
The scams floating around right now aren’t the sloppy emails we used to laugh at. These new ones are sharp. They use fancy tech and psychological tricks to bypass your gut instincts. But don’t worry. You don’t need to be a tech wizard to stay safe; you just need to know what the red flags look like.
Here is what is happening out there and how to keep your private life private.
1. The “Grandchild” Voice Clone (It’s Not Them)
You might remember the old version of this trick. Someone calls pretending to be a grandson in trouble. Usually, you could tell it wasn’t him because the voice was off.
Well, the game has changed.
Scammers are now grabbing snippets of audio from social media videos. If your grandchild posted a video on TikTok or Instagram, that is all they need. They use AI to clone the voice. When the phone rings, it sounds exactly like them. Same laugh, same tone. They will say they are in jail or stuck in Mexico and need money fast.
What to do:
- The Password Rule: Agree on a secret family password. If “Bobby” calls saying he is in trouble, ask for the password. If he can’t give it, hang up.
- Don’t Panic: Hang up and call their real cell phone number. Verify it yourself.
2. The “Computer Meltdown” Pop up
You are just reading the news or looking for a recipe, and suddenly BAM. A siren starts wailing from your speakers. A box pops up on the screen saying your computer is infected and you have to call “Microsoft” immediately.
It is terrifying, right? That is the point.
But here is the truth. It is all smoke and mirrors. Your computer is fine. The person on that phone line isn’t tech support; they are a thief waiting for you to open the front door. If you let them “remote in,” they will swipe your passwords or charge you for fixing a problem that didn’t exist.
What to do:
- Ignore the Number: Real companies like Apple or Microsoft will never put a phone number on a warning pop up. Never.
- The Hard Reset: If your mouse freezes, just hold the power button down until the screen goes black. Turn it back on, and the “virus” will be gone.
3. The Medicare “Chip Card” Trap
Medicare rules are a maze, and scammers know it. The latest trick? A friendly phone call telling you that you are due for a “refund” or a new “chip card.”
It sounds great, doesn’t it? But then comes the catch. To get the goods, they say they just need to “verify” your Social Security Number or your current Medicare ID.
What to do:
- Guard It: Treat your Medicare number like the combination to a safe.
- Check Your Vault: Don’t take a stranger’s word for it. If you keep your insurance details stored in a secure spot, like the InsureYouKnow.org portal, you can just log in and check your official policy. Call the number on your documents, not the one the stranger gave you.
4. The “Pig Butchering” Long Game
This one is nasty because it pulls on heartstrings. It usually starts with a “wrong number” text or a random message on Facebook. The person is nice. You start chatting. Over weeks, maybe even months, you become friends.
Then, they mention money. They are making a killing in crypto or gold, and they want to help you do the same. You might even put a little money in and see it grow on a website they send you. But the moment you invest a serious amount? The website vanishes, and so does your “friend.”
What to do:
- Keep Wallets Closed: Never take financial advice from someone you have only met through a screen.
- Do Your Homework: If they send a photo, run it through a Google Image search. You will probably find that picture belongs to a model or someone else entirely.
5. The Fake Government Threat
Fear is a powerful tool. Scammers love to pretend they are the IRS or the Social Security Administration. You will get a text or voicemail saying your account is “suspended” or you owe back taxes.
They will threaten arrest if you don’t pay right now. And weirdly, they often want payment in gift cards.
What to do:
- Gift Cards equal Scam: The government will never ask you to pay a fine with an Amazon gift card. That just doesn’t happen.
- Slow Down: They want you to panic so you stop thinking. Take a breath. It is almost certainly fake.
The Secret Weapon? Getting Organized.
Why do these scams work? Because they rely on chaos. They hope you don’t know where your real policy is. They hope you can’t find the right phone number to check if the story is true.
If you have your house in order, they can’t touch you.
When you have your vital info, like IDs, policies, and bank contacts, locked in a secure, encrypted hub, you have the power. If someone calls about your life insurance, you don’t have to guess. You log in, look at the real document, and you see the truth.
Stay Safe Out There:
- Verify, Verify, Verify: Don’t trust Caller ID.
- Lock It Up: Use a secure service to store your life’s paperwork.
- Buddy System: Share access to that digital vault with a family member you trust. It helps to have backup.
You don’t have to be paranoid to be safe in 2026. You just have to be organized.
Divorce & Data: How to Split Your Digital Life Safely
December 26, 2025

The Digital Aftermath
Breaking up used to mean splitting the vinyl collection and deciding who keeps the couch. Simple. Tangible. But today? The most complicated part of a separation isn’t sitting in the living room; it’s floating in the cloud.
We live online. A marriage in 2025 is basically a massive web of shared Netflix logins, joint bank apps, Amazon purchase histories, and thousands of photos on a server somewhere. This is the “Digital Split,” and honestly, it is messy. If people ignore it, they risk more than just awkwardness. They risk security leaks, drained accounts, and losing memories that actually matter.
Untangling this web takes a bit of grit, but it has to be done. Here is the playbook for separating a digital life without everything crashing down.
1. The Audit (Or: Seeing the Mess)
Before changing a single password, stop. Take a breath. You can’t fix what you can’t see. Most couples are far more digitally enmeshed than they realize. The first move is a simple audit.
Sit down and write it out. All of it.
- The Money: It’s not just the big bank account. Think Venmo, PayPal, crypto wallets, and those “buy now, pay later” apps.
- The Boring Stuff: Who pays the electric bill? Whose email is on the mortgage portal?
- The Fun Stuff: Spotify duos, Netflix profiles, gaming accounts.
- The Doorstep: Uber, Lyft, DoorDash.
Imagine the chaos if one person kills a shared credit card on Amazon without saying a word. Subscriptions bounce. Deliveries get canceled. It’s a headache nobody needs right now. Awareness is the best defense.
2. Locking the Virtual Doors
Once the list is ready, it’s time to secure the perimeter. Financial data is vulnerable, and emotions can make people do rash things.
For personal accounts like email, private checking, and social media, the passwords need to change. Today. And please, no more using the dog’s name or that old anniversary date. Pick something random.
This is also the moment to turn on Two-Factor Authentication (2FA) everywhere. It’s annoying, sure, but it’s a lifesaver. Even if an ex-partner guesses the new password, they can’t get in without the code sent to the phone. Also, dig into credit card apps and check for “authorized users.” If that isn’t cleared up, one person could be stuck paying for the other’s post-breakup therapy shopping.
3. The Photo Dilemma: Keep, Don’t Delete
This hurts the most. Who gets the pictures? The wedding video? The baby photos? Unlike a physical album, nobody has to lose out here.
The rule is strict: Duplicate, don’t delete.
Legally, wiping a hard drive or deleting a cloud account can be seen as destroying assets. It’s a bad look in court. Instead, buy a big external hard drive. Download everything, every shared memory, and hand the drive over. Or, use Google Photos to make a massive shared album, let them download it all, and then cut the link. Everyone walks away with their memories intact. No data lost.
4. Cutting the Invisible Ties
Then there are the things running in the background. The invisible tethers.
Check location sharing. Apps like “Find My” or Google Maps are great for knowing when a spouse is home for dinner, but after a split? It’s just surveillance. Unless there’s a solid reason to keep it on, like co-parenting coordination, shut it down.
The smart home is another trap. If one partner moves out, they shouldn’t still have the code to the front door or access to the Nest cameras. Watching an ex-partner come and go via a phone screen isn’t healthy for anyone.
5. The “Legacy” Check
It’s dark, but it matters. Check the beneficiaries.
Life insurance, 401(k)s, and investment apps all have that little “Transfer on Death” field. People fill it out once and forget it exists. If it isn’t updated, an ex-spouse could technically inherit money meant for kids or a new family ten years from now. It takes five minutes to fix, but it saves a lifetime of legal trouble later.
Final Thoughts
Separating a life is heavy work. But in this era, the digital separation is just as heavy as the physical one. It’s about privacy, security, and eventually, peace of mind. By locking down the data and safely copying the memories, the path forward gets a little bit clearer.
Pull the last three months of bank statements. That’s usually where the hidden subscriptions are hiding. Good luck.
Why Emailing Files to Yourself Is Not a Secure Strategy
December 17, 2025

It happens. A tax return needs saving. A passport needs copying. Time is short. The solution seems obvious: attach the file, type in the email address, and hit send.
Done. Safe. Accessible from anywhere.
Or so it seems.
That “Sent” folder feels like a private archive. In reality, it is a ticking time bomb. Cybersecurity pros don’t view email as a vault. They view it as a sieve. It leaks. And when it comes to the blueprints of a person’s life, wills, deeds, insurance policies, using email for storage isn’t just a bad habit. It is a security nightmare.
The Glass Envelope
Here is the thing about email. It feels private. It requires a password to log in, after all. But once a message leaves the draft folder, it travels across the open web. It hops from server to server.
Think of it less like a sealed letter and more like a postcard. The postman can read it. The sorting clerk can read it. Anyone who intercepts the mail truck can read it.
While big tech companies lock the front door, the data inside often sits in plain text. If a hacker guesses a password, or if the email provider has a breach, those attachments aren’t encrypted. They are just sitting there. Open. Readable. Ready to be stolen.
The Trap of “Searchability”
The best feature of email is also its biggest flaw. It is searchable.
Type “tax” into the search bar, and boom: five years of returns appear. Convenient for the user? Absolutely. But it is even more convenient for a thief.
When cybercriminals crack an account, they don’t scroll through boring updates from Netflix or Amazon. They run bots. These automated scripts hunt for gold. They scan for keywords like “SSN,” “Scan,” “Medical,” or “Deed.”
In three seconds flat, a hacker can scrape a decade of sensitive life data. That PDF of a driver’s license sent in 2019? The user forgot it. The hacker found it. And now, identity theft is just a few clicks away.
The “Whoops” Factor
Then there is the human element. We are clumsy.
Predictive text is great until it isn’t. A user starts typing “Sarah” to send a financial statement to a spouse. The computer autofills “Sarah” the realtor from four years ago. The “Send” button is hit before the brain catches up.
Too late.
There is no taking it back. A total stranger now holds the keys to a private financial life. It happens constantly. It is messy. And it is completely preventable.
The Fix: A Real Vault
If the inbox is a postcard, a Secure Digital Vault is a steel fortress.
This is why platforms like InsureYouKnow.org exist. They don’t just “store” files. They lock them down.
The difference lies in the math. Real security uses AES-256 encryption. Imagine taking a document and putting it through a shredder that turns it into millions of mathematical shards. The only person with the glue to put it back together is the account owner. Even if a thief stole the server, they would get nothing but digital noise.
Plus, a vault brings order to chaos.
When a crisis hits, a fire, a sudden hospital trip, nobody wants to dig through a mountain of spam to find an insurance policy. A vault keeps things sorted. Medical. Legal. Financial. Everything in its right place.
The Bottom Line
Convenience is a trap. Saving ten seconds by emailing a file is not worth the misery of untangling a stolen identity.
Vital documents don’t belong in the “Sent” folder. They belong behind a lock. So, go ahead. Search the inbox for “scan.” Delete the results. And put those files somewhere they actually belong.
What Happens to Your Digital Assets After You Die?
September 24, 2025
We spend so much of our lives online that it’s easy to forget just how much we’ve tucked away in digital spaces. Photos on Google Drive. A lifetime of emails. Bank apps, crypto wallets, even the music and books we’ve bought but never actually “own.” All of these things add up to what people now call your digital assets.
The tricky question is: what happens to them when you’re no longer here?
A Hidden Part of Your Estate
Think about how a traditional estate works. You leave a house, some savings, maybe a car, and your family knows how to claim those things. But with digital property, it is different. Passwords lock things up. Privacy laws keep companies from handing over your accounts. In many cases, providers do not even recognize heirs unless you have given explicit permission.
That means your online life, all those accounts and files, might just sit there untouched. Some platforms will eventually delete them. Others freeze them in time. And unless someone has the right access, even valuable things like cryptocurrency can disappear forever.
Why Families Struggle
It is easy to imagine the problems. Maybe your daughter knows you kept all the family photos in your Google account but cannot get past the two-factor authentication. Or perhaps you held a few thousand dollars in a crypto wallet that requires a private key only you knew. Even something as simple as canceling a subscription can be a nightmare if nobody has your login.
The result? Frustration, wasted time, and sometimes permanent loss.
The Law and the Fine Print
Adding to the confusion are the laws and service agreements. In many places, executors do not automatically get digital access. US states that follow a law called RUFADAA allow it only if you have given written consent, usually in your will. Big tech companies add another layer: Google lets you set up an Inactive Account Manager, Facebook has legacy contact settings, and Apple has its own Digital Legacy program. If you do not turn those on, your family may have no options.
So between legal barriers and tech restrictions, the default outcome is often nothing happens and accounts remain locked away.
How You Can Plan Ahead
The solution is not complicated, but it does take a little thought:
- Make a list of important accounts. It does not have to be detailed, but your family should at least know what exists.
- Decide who should handle them. Pick someone you trust and tell them they will be your digital executor.
- Write it into your will. A line or two giving that person authority can make a big difference.
- Use built-in tools. Set up legacy contacts where available. It only takes a few minutes.
- Keep access information safe. A password manager with emergency access, or a sealed note in a safe, works better than trying to share details in casual ways.
The key is to make sure someone you trust knows how to act when the time comes.
One practical way to protect your digital legacy is by using a secure service like InsureYouKnow. It allows you to store important documents, account information, and passwords in a safe, encrypted digital vault. You can control who has access and receive reminders to keep your records up to date, making it easier for your loved ones to manage your digital assets according to your wishes.
Why It Matters
Digital assets are not just about money. Sure, cryptocurrency or an online business can carry real financial weight, but the sentimental side matters just as much. Family photos, voice notes, or personal letters stored in an inbox can be treasures to those you leave behind. Without a plan, those things may vanish into the cloud forever.
By setting aside an hour or two to prepare, you can spare your loved ones unnecessary stress and give them access to the parts of your life that matter most.
